What Is Smooshing?
The word sounds almost playful — “smooshing” — but the reality is anything but. Smooshing is the consumer-friendly term now being used to describe SIM swap fraud, a form of identity theft in which a criminal hijacks your phone number by convincing your mobile carrier to transfer it to a SIM card the criminal controls.
Once your number is in their hands, every text message sent to your phone — including the one-time passwords and verification codes that protect your bank accounts, email, and crypto wallets — goes straight to the attacker. Within minutes, victims can find themselves locked out of their own accounts while criminals drain them dry.
The term “smooshing” has been popularized by credit unions and consumer protection organizations as a way to make SIM swap fraud more recognizable to everyday people who might not be familiar with technical jargon. But whatever you call it, the damage is very real.
How Smooshing Differs from Classic SIM Swap
Traditional SIM swap fraud focused primarily on physical SIM cards. A criminal would walk into a carrier store, claim to be you, and walk out with a new physical SIM card loaded with your number.
Smooshing has evolved. Today’s fraudsters exploit both physical SIM swaps and port-out fraud — where your number is transferred entirely to a different carrier — as well as a newer vector: eSIM hijacking. eSIMs are digital SIM profiles embedded directly in modern smartphones. A criminal can request a remote eSIM QR code from your carrier without ever visiting a store, making detection far harder and the fraud harder to reverse.
Research shows that 96% of SIM swap cases involve social engineering or insider collusion, not sophisticated hacking tools. The weak link is almost always a human being at a call center or retail location — and criminals have gotten very good at exploiting it.
Step-by-Step: How a Smooshing Attack Unfolds
Understanding the exact playbook criminals use is the first step to defending against it.
Step 1: Harvesting Your Personal Information
The attacker begins collecting data on you — often using a combination of your social media profiles, data breaches, and phishing campaigns. They’re looking for your full name, address, phone number, date of birth, and answers to common security questions (“What was the name of your first pet?”). This information is often available for as little as a few dollars on dark web markets.
Step 2: Impersonating You to Your Carrier
Armed with your personal details, the attacker contacts your mobile carrier. They claim to be you — usually with a story like “I lost my phone and need an emergency SIM replacement” or “I just bought a new phone and need to transfer my number.” In 2025, criminals are increasingly using AI-powered voice cloning to sound more convincing, mimicking how you might actually speak.
Step 3: The Number Transfer
If the carrier representative is convinced — or in some cases, bribed — they authorize the SIM transfer. From that moment on, your phone number belongs to the attacker. Your own phone loses signal, often the first sign something is wrong.
Step 4: Account Takeover
With control of your phone number, the attacker triggers “forgot password” requests on your financial accounts. The one-time codes arrive on their device. Within minutes, they change passwords, lock you out, and begin draining accounts.
Step 5: The Damage
Crypto wallets, bank accounts, and email are the most common targets. In some cases, attackers use compromised accounts to request wire transfers or access business accounts.
The FBI Numbers: 982 Complaints, $26 Million Lost
The FBI’s Internet Crime Complaint Center (IC3) documented 982 SIM swap complaints in 2024, resulting in nearly $26 million in losses. While down from the $72 million peak in 2022, the 2024 figures represent a deeply damaging average loss of more than $26,000 per victim — a life-changing sum for most households.
The global picture is even starker. In the UK, fraud prevention service Cifas reported a 1,055% increase in unauthorized SIM swaps in 2024, with nearly 3,000 cases compared to just 289 the year before. In Australia, IDCARE reported a 240% increase in people seeking help for SIM swap fraud in the same period, with 90% of cases occurring without any direct engagement from the victim.
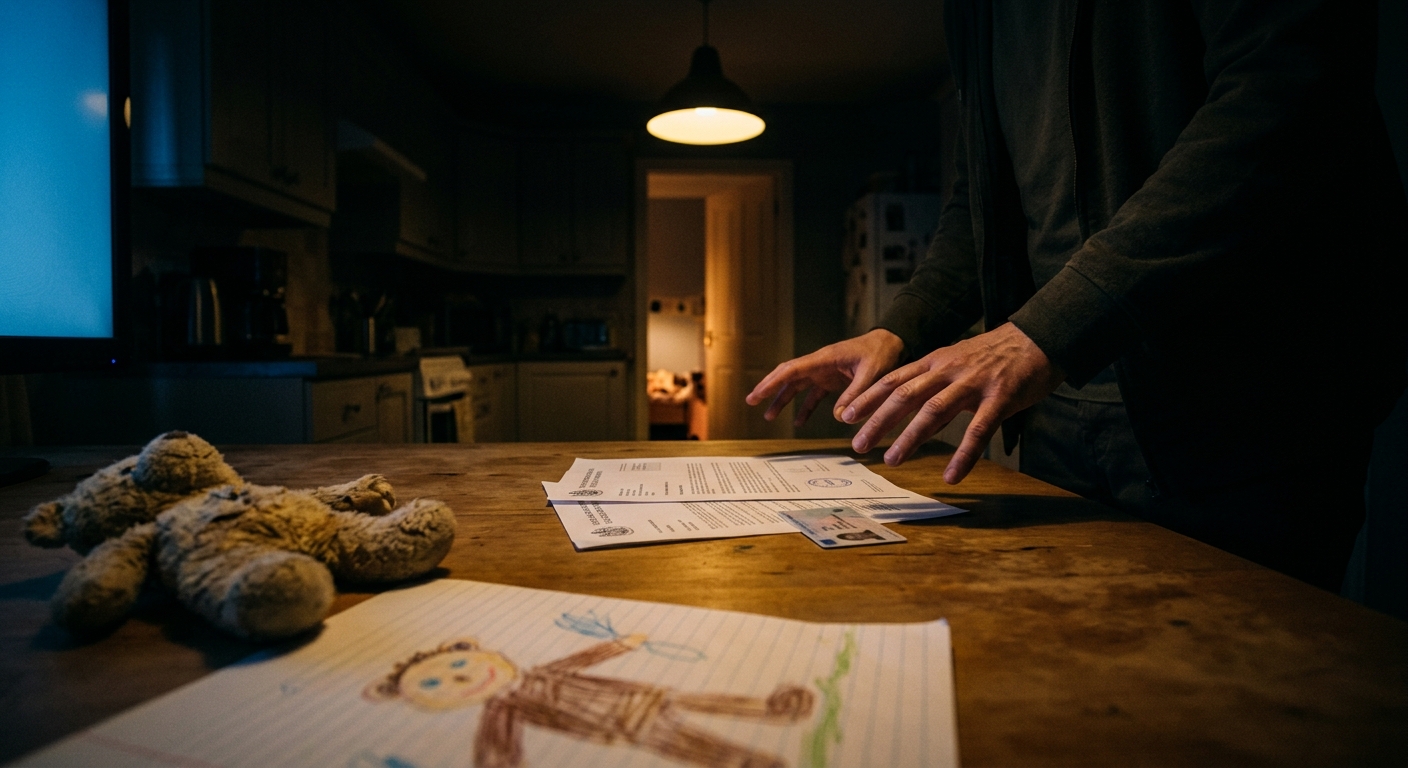
Real Victims, Real Losses
One of the most high-profile recent cases came in March 2025, when a California arbitrator ordered T-Mobile to pay $33 million after a SIM swap enabled thieves to steal approximately $38 million in cryptocurrency from a customer’s account. The attackers bypassed the customer’s “extra security” measures by convincing a T-Mobile call center agent to issue a remote eSIM QR code — entirely over the phone, without ever visiting a store.
In another well-known case, Twitter co-founder Jack Dorsey had his own Twitter account hijacked via a SIM swap in 2019, proving that even high-profile, technically sophisticated individuals can be victimized. The attack required no hacking of Twitter’s systems — just a phone call to his carrier.
Carrier Protections: What Boost, TracFone, and Consumer Cellular Offer
In November 2023, the FCC introduced rule FCC 23-95, requiring wireless carriers to implement stronger authentication before processing SIM swaps or port-out requests. Several carriers have gone further with specific consumer protections:
Boost Mobile now requires a port-out PIN before any number can be transferred to another carrier. Customers can set and change this PIN directly in their account settings.
Consumer Cellular sends text alerts when a number transfer is requested and allows customers to place a temporary hold on their account if they suspect a breach.
TracFone offers customers the ability to lock their account against port-out requests and requires additional verification for SIM-related changes.
T-Mobile, Verizon, and AT&T all offer account-level security features including port-out PINs, account locks, and “NOPORT” flags — though as the 2025 T-Mobile arbitration case showed, human error can sometimes override even these measures.
The key takeaway: these protections only work if you activate them. Log in to your carrier account today and look for SIM swap or port-out security settings.
How to Protect Yourself
Smooshing attacks are frightening but largely preventable with the right precautions.
1. Add a Port-Out PIN or Account Lock to Your Carrier Account
Log into your wireless carrier’s website or app and look for SIM swap or port-out security settings. Add a PIN or security passphrase. Enable account locks if available. Do this today — don’t wait.
2. Switch Away from SMS-Based Two-Factor Authentication
Text message codes are exactly what smooshing is designed to steal. Wherever possible, use an authenticator app (like Google Authenticator, Authy, or Microsoft Authenticator) instead of SMS codes. These apps generate time-based codes locally on your device and cannot be intercepted via a SIM swap.
3. Use a Security Key for Critical Accounts
For your email, financial accounts, and any accounts with access to your money or identity, consider adding a hardware security key (like a YubiKey). These physical devices must be present to log in — no phone number required.
4. Minimize Your Digital Footprint
Limit what personal information is publicly available on social media. Remove or lock down posts that reveal your phone number, hometown, birthday, or mother’s maiden name — all common ingredients in social engineering attacks.
5. Set Up Fraud Alerts with Your Bank
Ask your bank to flag any account changes, large transfers, or login attempts from new devices. Some banks allow you to set spending limits or require in-branch verification for large wire transfers.
6. Monitor Your Phone Signal
If your phone suddenly loses service in an area where you normally have strong signal, act immediately. Call your carrier from another phone, report that you may be a SIM swap victim, and ask them to freeze your account while they investigate.
7. File a Report if You’re Victimized
Report SIM swap fraud to the FBI’s IC3 at ic3.gov, the FTC at reportfraud.ftc.gov, and your state attorney general’s office. Quick reporting can help law enforcement track patterns and sometimes recover stolen funds.
Smooshing may sound like a minor inconvenience, but its consequences can be devastating. With a few proactive steps, you can make yourself a much harder target — and keep your phone number exactly where it belongs: in your hands.