651 Arrests. $4.3M Recovered. 1,442 Servers Torn Down. This Is What Rails Warfare Looks Like.
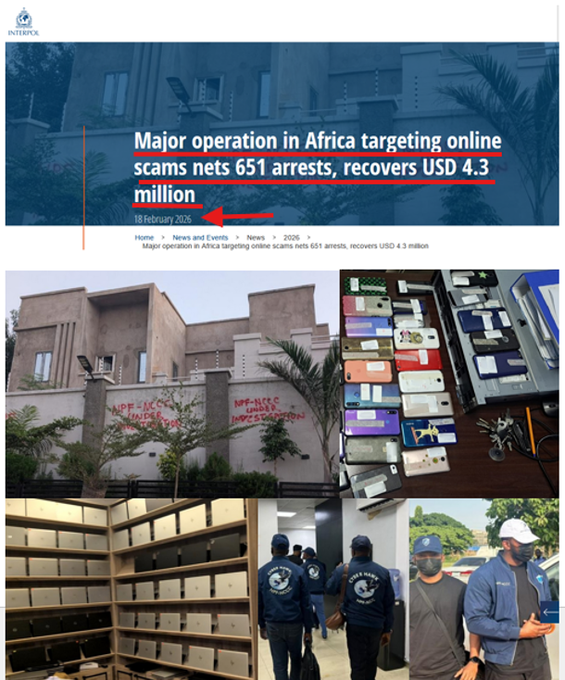
When INTERPOL announced Operation Red Card 2.0 on February 19, 2026, the headlines led with the arrest count. Fair enough — 651 suspects across 16 African nations in eight weeks is a number worth stopping for. But the headline is almost a distraction from what actually happened here. This wasn’t a bust. It was a demolition. And if you’re watching the Global Purge unfold in real time, you already know the difference.
DOJ Targets Starlink Terminals at Myanmar Scam Compounds — What Cybersecurity Professionals Need to KnowThe U.S. Department of Justice just made a move that signals a significant evolution in how American law enforcement approaches transnational cybercrime infrastructure — and it goes straight to the satellite dish on the roof. In November 2025, federal magistrate judges authorized seizure warrants targeting Starlink satellite terminals and accounts![]() ScamWatchHQScamWatchHQ
ScamWatchHQScamWatchHQ
What They Did
From December 8, 2025 through January 30, 2026 — fifty-four days — law enforcement agencies from Angola, Benin, Cameroon, Côte d’Ivoire, Chad, Gabon, Gambia, Ghana, Kenya, Namibia, Nigeria, Rwanda, Senegal, Uganda, Zambia, and Zimbabwe ran a coordinated strike under the banner of the African Joint Operation against Cybercrime (AFJOC).
The final numbers:
- 651 arrests- USD $4.3 million recovered- 2,341 electronic devices seized- 1,442 malicious IPs, domains, and servers taken down- $45 million+ in documented victim losses- 1,247 victims identified — predominantly African, but spanning multiple regions
The operation targeted three converging fraud verticals: high-yield investment scams, mobile money fraud, and fraudulent mobile loan applications. In practice, those three categories are the same machine with different faces. Fake returns on fake investments. Fake loan apps harvesting real biometric data and then extorting users with it. Mobile money rails used as the payment layer for everything.
This is the second phase of Red Card. Phase one, which ran from November 2024 through February 2025, netted 306 arrests and 1,842 seized devices. Phase two more than doubled that. The operation is scaling. So is the threat. For the full picture of how 2025 shaped the global enforcement landscape, our 2025 Global Scam Landscape year-in-review documented INTERPOL’s parallel operations — including Operation Serengeti 2.0, which netted 1,209 arrests across 18 African countries and recovered $97.4 million, and Operation Contender 3.0, which dismantled 81 criminal infrastructures across 14 African nations.
Rails Warfare: Why This Is Different
Most cybercrime enforcement goes after the scammer. Red Card 2.0 went after the factory.
There’s a critical distinction in how transnational fraud ecosystems actually function. The individual scammer — the kid typing phishing messages in a boiler room — is replaceable in 48 hours. The infrastructure beneath them is not. SIM banks, compromised telecom access, social-engineering operation hubs, fake investment dashboards, fraudulent app distribution channels, and the money-movement rails that connect all of it — that’s the real target, and that’s what Red Card 2.0 dismantled.
In Nigeria, investigators didn’t just arrest people. They took down over 1,000 fraudulent social media accounts, raided a residential building that had been converted into an operational fraud hub, and cracked a phishing-to-crypto pipeline that used young recruits to execute identity theft and fake digital asset investments. As we’ve documented in detail, Nigeria’s fraud ecosystem is organized, stratified, and deeply rooted — the country ranks fifth globally in cybercrime and its operators have extracted an estimated $26 billion annually from victims worldwide through BEC, romance scams, and crypto fraud. Red Card 2.0 hit the supply chain that feeds that machine.
Nigerian authorities also arrested six individuals who had infiltrated the internal platform of a major telecommunications provider using compromised employee credentials — and were siphoning large volumes of airtime and data for illegal resale. That’s not a scammer running a fake Instagram. That’s a threat actor with insider access rewriting the economics of the telecom stack. That’s infrastructure-level compromise.
In Kenya, 27 suspects were running investment fraud through messaging apps and social media, showing victims falsified dashboards and blocking all withdrawal requests — a playbook so standardized it could run on a franchise model. This is the same attack surface we mapped in depth in our Kenya M-Pesa fraud investigation: a nation where 9.8% of mobile money users have experienced direct financial loss, SIM swap fraud has exploded 327%, and fraud now accounts for 23% of all digital banking crimes in the sub-Saharan region. The 27 arrests in Red Card 2.0 represent enforcement catching up to a threat we documented months ago.
In Côte d’Ivoire, 58 arrests tied to predatory mobile loan apps: deceptive promises of quick credit, hidden fees, abusive debt collection, and aggressive harvesting of personal data. The apps were the delivery mechanism. The personal data was the secondary product.
And Ghana — one of the Red Card 2.0 participating nations — brings its own documented dimension. The Sakawa phenomenon we covered in December 2025 sits directly in the operational profile Red Card 2.0 targeted: Ghanaian cybercrime operations have stolen over $100 million from Western victims through romance scams and BEC attacks, with the criminal subculture now penetrating music, fashion, and social media.
This is the modern transnational fraud stack, and Red Card 2.0 hit it at every layer simultaneously.
The Coalition Stack: Private Intel, No Flag
The most significant structural development in Operation Red Card 2.0 isn’t the arrest count. It’s who fed the intelligence that made those arrests possible.
INTERPOL’s named partners for this operation:
- Trend Micro — threat intelligence, malware ecosystem mapping- TRM Labs — blockchain analytics and crypto transaction tracing- Team Cymru — internet infrastructure threat intelligence- Uppsala Security — crypto forensics and transaction risk analysis- Cybercrime Atlas — cross-sector threat intelligence sharing consortium
This is the modern coalition stack in its most visible form: cyber intelligence companies feeding forensic data directly into law enforcement operations across sovereign borders, in real time, with no single government controlling the intelligence layer.
TRM Labs traces money moving through crypto rails — the same rails pig butchering operations rely on to move billions out of victims’ hands and into layered crypto wallets. Team Cymru maps the infrastructure — who owns the IPs, what the servers are doing, where the command-and-control is routing. Trend Micro correlates malware families and campaign fingerprints across millions of endpoints. Uppsala Security follows the blockchain breadcrumbs into the exits. Cybercrime Atlas aggregates the threat picture from private sector contributors across industries.
The law enforcement agencies then execute based on that fused intelligence picture. The arrests and raids are the visible output of an invisible analytical machine that runs continuously across private-sector networks.
This is not a future state. This is operational now, and Red Card 2.0 is the clearest documented example of it running at scale. The crypto tracing component is especially significant — cryptocurrency investment fraud generated an estimated $9.9 billion in scam revenue in 2024 alone, and the financial intelligence pipeline from companies like TRM Labs is increasingly the tool that makes these operations traceable and actionable.
16 Nations, Same Fingerprints, Same Sequencing
One of the defining characteristics of transnational fraud operations is that they look identical regardless of geography. The same fake investment platforms. The same falsified dashboard aesthetics. The same script for blocking withdrawals. The same SIM farming toolkits. The same mobile loan app architecture used to harvest biometric data.
This standardization is the fraud industry’s efficiency feature. It’s also its forensic signature.
When 16 African nations are able to coordinate simultaneous enforcement actions against networks that share infrastructure, tooling, and operational playbooks, it means they’re working from the same intelligence picture. That’s what AFJOC built. That’s what the private sector partners enabled. The sequencing of raids across national borders within the same eight-week window — without any single nation tipping off the network — is a serious operational achievement.
It also tells you something about how the threat operates. These networks are not independent criminal enterprises running in isolation. They share back-end infrastructure. They recruit from the same pools. They move money through the same rails. The cross-border coordination of enforcement is a direct mirror of the cross-border coordination of the fraud itself.
The social engineering factories are particularly standardized. Whether it’s romance scams running through messaging apps in Kenya or investment fraud hubs in Nigeria, the psychological playbook is identical. Our coverage of vishing and social engineering scams documents how this industrialization of manipulation has scaled — and why no country is isolated from it. The South Africa cybercrime report — covering a nation hemorrhaging R2.2 billion ($118 million) annually — shows the same standardized attack patterns showing up across the continent regardless of language or jurisdiction.
The Funding Architecture and What It Signals
Operation Red Card 2.0 was funded by the UK’s Foreign, Commonwealth & Development Office through AFJOC, with additional operational support from GLACY-e — the Global Action on Cybercrime Enhanced project, a joint initiative of the European Union and the Council of Europe.
That funding structure matters. Western governments are not funding African cybercrime enforcement out of altruism. The victim pool documented in Red Card 2.0 spans multiple regions — African victims, yes, but also victims “from other regions of the world.” The fraud rails that originate in West African boiler rooms route through crypto exchanges in Eastern Europe, payment processors in Southeast Asia, and money mule accounts in the UK and United States. The UK and EU are funding enforcement at the source because they are downstream victims.
This is the economic logic behind the coalition: the cost of prevention at the origin point is lower than the cost of loss at the destination. It’s insurance math applied to transnational enforcement. The 2025’s Most Expensive Scams analysis quantified what that downstream damage looks like for American victims alone: investment fraud costs Americans a median of $9,000+ per incident, with crypto the preferred payment rail because it’s irreversible. Every server Red Card 2.0 took down in Lagos or Accra is one fewer pipeline draining retirement accounts in Manchester or Minneapolis.
Context: Where This Sits in the Purge Cadence
Red Card 2.0 didn’t happen in isolation. In November 2025, INTERPOL and AFRIPOL ran a separate operation uncovering a $562 million crypto fraud network spanning 17 countries, with $260 million linked to suspected terror financing — 83 arrests, $600,000 seized. That operation established the financial scale of the threat. Red Card 2.0 hit the operational layer beneath it.
These operations are not independent events. They are sequential pressures applied to interconnected systems. The intelligence generated from Phase 1 of Red Card fed Phase 2. The crypto tracing from the November operation informed the financial targeting in Red Card 2.0. Each action generates intelligence that seeds the next one.
This is the Global Purge cadence: not one big takedown, but sustained, cumulative pressure on the entire ecosystem — arrests, infrastructure demolition, financial recovery, and intelligence fusion — running in rolling waves across jurisdictions. Our 2026 Scam Trends guide flagged scam-as-a-service networks as one of the defining threats of the year ahead — industrialized fraud infrastructure sold to less technical criminals. Operation Red Card 2.0 dismantled operational nodes in exactly that ecosystem.
The question enforcement will face in Phase 3 is regeneration speed. As one analyst tracking African cybercrime enforcement put it: scam ecosystems regenerate quickly. The talent pool is large, the toolkits are commoditized, and the financial incentives outpace enforcement consequences in many participating nations. The arrests are the visible metric. The infrastructure takedowns are the durability metric. And the private intelligence integration is the sustainability metric.
Red Card 2.0 scored well on all three. Whether that holds across the regeneration cycle is the operational question that matters.
Bottom Line for Security Practitioners
If you’re advising clients in financial services, telecom, or any sector with mobile payment exposure in African markets, Red Card 2.0 is a signal, not a solution. The enforcement operation confirmed what threat intelligence has been mapping for two years: mobile money rails, telecom insider access, and fake investment platforms are the primary attack surface for transnational fraud originating from this region.
The telecom infiltration case from Nigeria — six individuals accessing a major carrier’s internal platform through compromised staff credentials — should be a direct trigger for any telco or enterprise with operations on the continent to review privileged access controls, credential hygiene for third-party and contractor accounts, and airtime/data anomaly detection. That attack vector is not unique to the arrested group. It’s a technique being used across multiple threat actors. Kenya’s M-Pesa fraud crisis — where Safaricom fired 113 employees for fraud violations and SIM swap fraud investigations exploded 327% in a single year — demonstrates what happens when that vector isn’t controlled early.
For anyone tracking the private-sector-to-law-enforcement intelligence pipeline: Trend Micro, TRM Labs, Team Cymru, Uppsala Security, and Cybercrime Atlas are now documented contributors to active enforcement operations producing arrests and infrastructure takedowns. That’s not a marketing claim. That’s an INTERPOL press release. The fusion model works, and it’s accelerating.
For consumers: if you’ve been targeted by high-yield investment offers through messaging apps, fake loan applications, or social media “opportunities” with blocked withdrawals, the ScamWatchHQ Scam Hub documents the full taxonomy of fraud types, and the Resources page lists reporting channels across every major jurisdiction.
Watch for Phase 3.
ScamWatchHQ covers the Global Purge — the coordinated, multi-jurisdictional enforcement campaign dismantling transnational fraud infrastructure. For consulting inquiries on mobile fraud exposure, telecom threat surface assessment, or financial crime intelligence, contact QSai LLC.



